Reading time: 8 minutes
Ransomware has become one of the highest revenue-generating crimes we’ve ever seen. Last year, 2021, was a record year for ransomware attacks. According to Crowdstrike, the average demand was $6 million. Additionally, the Secretary of Homeland Security Alejandro Mayorkas stated, “50 to 70% of ransomware attacks were aimed at small and medium-sized companies.” From the looks of things, bad actors have their foot on the gas and aren’t letting up anytime soon.
Why are we seeing ransomware demands increasing so dramatically over the past three years?
First, ransomware is a big money business. Cybersecurity Ventures predicted that ransomware would cost $6 trillion annually in 2021. These numbers are expected to increase in 2022.
Second, there are more businesses online than ever before. A bad actor has significantly less risk exposure in attacking a cloud-based business than, say, robbing a jewelry store.
Finally, when it comes to entering the ransomware industry, barriers are extremely low. The idea of a faceless cybercriminal in a black hoodie is no longer the case. All you need is a laptop and a high-speed internet connection. Malicious actors have access to resources, tools, and services like never before.
One of these services is a “done for you” business model called, Ransomware-as-a-Service (RaaS).
What is Ransomware-as-a-Service?
Ransomware-as-a-Service borrows best practices from the Software-as-a-Service (SaaS) business model. This provides a subscription-based platform for ransomware code builders to collaborate with threat actors lacking the technical knowledge to create ransomware.
How does RaaS work?
RaaS works like any franchise-like or affiliate-based business model. A technical cybercriminal (The seller) writes the ransomware code and rents it to other malicious actors (the buyers). The buyers rent or lease the ransomware under an affiliate program. The seller provides technical knowledge and step-by-step documentation on how to launch a ransomware attack using their service. The seller will also provide a real-time dashboard for the buyer to check on the status of the ransomware attack. Once the ransom’s paid, the money is split between the service provider, the coder, and the attacker. This business model is so enticing that RaaS providers advertise their services over the dark web.
Here is a table from Crowdstrike.com, outlining the RaaS process in detail:
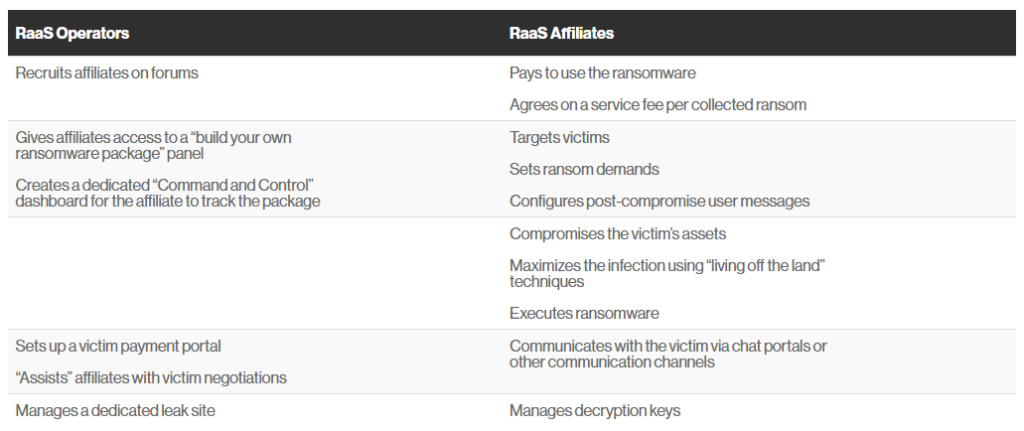
This is a win-win situation for both the seller and the buyers. First, the seller earns quick cash per transaction. Second, the buyers don’t need to write the malicious code. Their only job is launching the cyberattack onto their unsuspecting victims and collecting their money. Third, once the job is over and everyone’s compensated, all parties are free to go their separate ways.
How did RaaS grow so quickly?
The COVID-19 pandemic helped usher in this new wave of RaaS ransomware attacks. So much so that researchers at cybersecurity company Group-IB reported that almost two-thirds of ransomware attacks analyzed during 2020, came from cyber criminals operating on a RaaS model. “Companies had to provide their employees with the capability to work remotely and we saw an increase in the number of publicly accessible RDP servers. Of course, nobody thought about security and many of such servers became the points of initial access for many ransomware operators,” said Oleg Skulkin, senior digital forensics analyst at Group-IB. Threat actors found a vulnerability and created a service to monetize it.
Malicious actors came out of the woodwork to capitalize on these flourishing opportunities. As more and more cyberhackers took advantage of this expanding industry, the demand for ransomware services skyrocketed even further. Threat actors learned that they needed help to carry out these lucrative breaches. This opened up new opportunities for cyberhackers to work with one another.
Highly qualified threat actors banded together to form several ransomware groups. The cyber-terrorist crews attacked at will, and increasingly flaunted their wins. As those black hat groups’ notoriety increased, so did the target on their backs. For instance, Conti, is a Russian ransomware criminal enterprise, and well respected in the cyberhacker community. This organized crime organization employed over 100 salaried employees and generated over 100 million dollars in annual revenue. From the outside looking in, Conti is at the top of the ransomware food chain. However, even Conti isn’t immune to a premediated cyber penetration.
On March 1, 2022, an unknown Ukrainian researcher infiltrated Conti’s internal chat logs and additional sensitive data, according to a recent article from Krebs on Security. Conti’s criminal enterprise operations were brought to light by compromised confidential internal records. One of the key findings revealed how Conti dealt with its own internal breaches and attacks from private security firms and foreign governments. It just comes to show that even threat actors are at risk of being compromised, just like everyone else.
What does your company stand to lose from a RaaS attack?
Revenue
Obviously, the financial implications of a ransomware attack are significant. A ransom costs anywhere from several thousand to upwards of millions of dollars. The bigger the impact on an organization, the bigger the payoff.
Reputational Damage
When your company’s reputation is diminished, it can take years to rehabilitate its image. If your organization is in the financial sector, your customers are paying for the security of their confidential financial investment. A bank patron may consider safer options, regardless of whether or not your bank had preventive, cybersecure safeguards in place.
If word gets out to the public, just the perception of an unsecure financial environment is enough to ignite a mass exodus of customers to your competitors.
How can your organization protect itself from a RaaS attack?
There are several preventative measures you should have in place to protect your business. In fact, we’ve shared a few of those methods in our recent ransomware blog. While those security steps will secure most of your company, you still will need a robust cybersecurity program to further protect your organization from highly motivated bad actors.
Here are a few of the multi-level protections that Cooperative Systems provides to protect your company from the next ransomware attack:
- Multi-Factor Authentication
- Encryption
- Anti-ransomware software
- External vulnerability testing
- Security awareness training for employees
To learn more about our additional enhanced cybersecurity offerings, click here.
