A recent 2021 phishing study reported that the cost of phishing more than tripled since 2015. The average annual cost of phishing increased from $3.8 million in 2015 to $14.8 million in 2021.
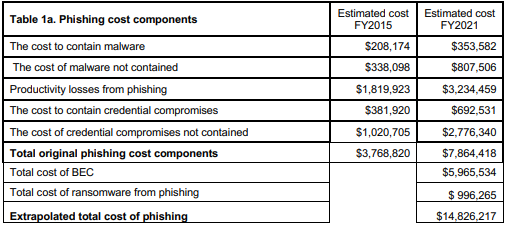
Source: Ponemon Institute’s The 2021 Cost of Phishing Study
In addition to these rising organizational costs, it also stated that nearly 65,343 wasted annual hours were attributed to these phishing attacks.
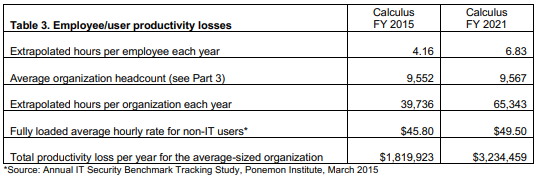
Source: Ponemon Institute’s The 2021 Cost of Phishing Study
Larry Ponemon, Chairman and Founder of the Ponemon Institute, states that “most of the costs incurred by companies come from lost productivity and remediation of the issue rather than the actual ransom paid to the attackers.”
Breaches are expensive all around and it pays to avoid them. The best way to prevent breaches is to invest your IT budget on cybersecurity awareness training and phishing email testing for your employees.
According to CisoMag, “On average, security awareness training reduces phishing expenses by more than 50%.”
Here are key ways to help your team quickly identify and report phishing tactics.
Phishing tactics work because they exploit our emotions.
Employees can recognize phishing patterns quicker by understanding the human emotions a hacker will exploit:
- Urgency: The email wants a user to act now. When we act urgently or impulsively, our reasoning brain doesn’t have enough time to question whether the email is legitimate or not.
- Plausibility: Phishing emails are written in real-life and everyday situations, making them more relatable and therefore, believable to the reader.
- Familiarity: Emails that claim to be from a trusted authority figure or a well-known organization tend to get our attention more. This approach is a specific type of phishing email known as, spear phishing.
Phishing emails tend to rely on specific language patterns that try to profit off your fears.
There are many common terms used in a phishing email. Here are a few good examples:
- “You are in direct violation of company policy”
- “If you do not comply within the next 24 hours, your account will be permanently deleted.”
Along these lines and according to Security Magazine, these types of emails may also ask you to do any of the following: ask you to fix a problem with your account or payment information, ask you to confirm your personal information or send you a fake invoice to instill curiosity (and trick you into opening it and/or responding).
Be sure to always double check and verify the source of these emails before responding by calling your credit card company, your local government or whomever the stated authority is in the email. Be sure to NOT use the contact information in the suspicious email and instead search Google or other trusted sources.
Phishing emails promise free things because everyone loves free things.
Again, we’re only human. We have emotions. We enjoy winning and getting free items. Unfortunately, malicious actors use these very things against us and include free offers and refunds in phishing emails.
Examples include emails that offer you a free coupon, free gift, government refund, etc. If you see any of these mentioned in an email, immediately question the intent and report it to your company.
Now that you know how to identify phishing emails via their use of content to manipulate your emotions and behavior, here are quick ways to instantly know if it’s a phishing email.
In a recent panel of information security experts, Jared Schemanski, Security Analytics Team leader for Nuspire Networks suggested these quick ways to identify suspicious emails:
Test the authenticity of the email sender and email links.
- Drag your cursor over the email sender, as well as any links in the email. If the links are malicious, they will probably not match up with the email or link description.
Be alert to fraudulent URLs in the address bar
- Read the address bar’s URL from right to left.
- The last website address is the true domain.
- Fraudulent URLs will not include HTTP, and will begin with an IP address.
Question the validity of an email by directly calling or emailing* the sender.
*Keep in mind that sometimes a sender’s email or social media accounts were hacked so it might be best to call or text the sender directly.
We’d like to reiterate that the best way to prevent phishing emails from leading to security breaches is to train and test your employees in how to spot and report phishing emails.
The best way for employees to learn and integrate cybersecurity awareness is to practice what they’ve learned. According to Felix Odigie, CEO of Inspired eLearning, for employee phishing awareness to improve, organizations need regularly test employees with fake phishing emails. This enables the employees to recognize phishing emails especially when new types appear in circulation. After each phishing email test, staff will receive a follow-up email notifying them of the test and reinforcing the core concepts that will continue to improve their ability to spot and report these schemes.
Equipping your employees with the proper resources and training is critical to protecting your business. If you’re interested in learning more, click here.
