The data inside your business is worth far more than you might think.
Not to mention the Cyber security-health of your company is worth just as much as your business data.
Everywhere you go on the web, you are leaving digital breadcrumbs for attackers to follow to learn about you, acquire your information and data, and infiltrate your privacy.
We encountered the below featured infographics via one of our favorite Cybersecurity blogs, Krebs on Security, and we felt that we must absolutely share with our readers to drive home this fact:
If you’re asking yourself ‘is Cyber security important and do hackers really want my business data‘ the answer is yes.
Your seemingly simple and isolated data is valuable to hackers, and here’s how and why.
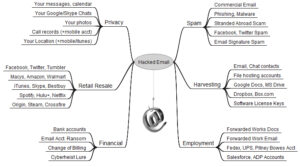
The Value of a Hacked Email Account
With access to your email account, a hacker could go in a number of directions to exploit you and your information, gaining valuable insights along the way to further infect your life.
- They’ll go after your contact lists, blasting them from your address asking for money and for them to click links, thereby forfeiting their security.
- They’ll sift through your archives and saved messages for any relevant data to gain access to your other accounts with credentials, hints about your identification, credit information, and so on.
- They’ll reset passwords and field the reset prompts to lock you out of your own accounts and gain full control.
From there, they can destroy your virtual identity and kill the Cyber security efforts you’ve work hard to establish, in an instant.
The Value of a Hacked Computer
Similar to email hacking scenarios, but often much graver, once hackers take over your user profile they are privy to the whole host of files, logged in accounts, email and chat clients, and private connections that your workstation facilitates for you day-to-day. At this level, hackers can go so far as to begin to even host illegal operations and scamming from your very machine and account.
How They Get In
There are countless ways for malware to weasel its way into your machine or accounts, and over 45% of all malware is facilitated by social engineering, which means that users are persuaded or tricked into letting them in. This alludes to malware, or “malicious software”.
When you click unidentified and suspicious links, navigate to untrusted sites, open unknown attachments, install applications or add-ons from unknown sources, and other such choices, you immediately put your sensitive information at risk.
Once malware finds the door or window into your network, data, or account, the way it gets hold of your data or machine depends on its type. Here are a couple of types of malware and a brief description of how they work:
- Trojans look like harmless add-on programs on your machine, but they can really damage your host systems. They don’t replicate, but they steal passwords and other data of value.
- Viruses exploit security vulnerabilities and attach themselves to programs and replicate and spread across your machine, and even across your network in some cases. They can add and delete files and folders, reformat portions of your hard drive, and of course facilitate leaking of data via backdoors.
- Worms spread across entire networks, replicating code and facilitating data breaches and manipulation of data by way of backdoors.
What Can Malware Do?
Here are some possible scenarios that detail how malware might “work” once it finds its way onto your machine or into your network:
- Block access to certain programs and forcing the user to remit payment to regain access
- Replicate itself across your system to act as a data-gathering net
- Add unwanted programs and add-ons that annoy the heck out of you to click them, which would give the attacker access to your data and systems to damage the host or exploit you
- Set up triggers that, if manipulated when you take certain actions on your machine, can completely wipe your hard drive or allow them access to pipelines of data
Train Your Team To Block Social Engineering
Cooperative Systems can train and test your employees to ensure that they’re prepared and informed to block attempts to exploit their accounts and your priceless data. Contact us here to learn how.
Check out these other posts for more information on how to prevent social engineering attacks on you and your business:
Every User Should Know NOT To Do These 3 Things