Blog
Stay current with the latest in technology and cybersecurity.
“We have antivirus, so we’re covered.”“Hackers only go after large companies.”“That’s IT’s job, not mine.”“If we get hit, our cyber insurance will handle it.” Sound familiar? If so, you’re not alone. These are just a few of the most common cybersecurity myths that businesses continue to believe. And unfortunately, they create a false sense of…
Beware of These 3 Trending Social Engineering Scams
What is social engineering As more businesses transition to remote work and operating from a cloud, threat actors have discovered the biggest weak point in their cybersecurity—the employees. Social engineering is a tactic used by criminals designed to abuse human emotions such as empathy or fear to convince an unsuspecting victim to do any desired…
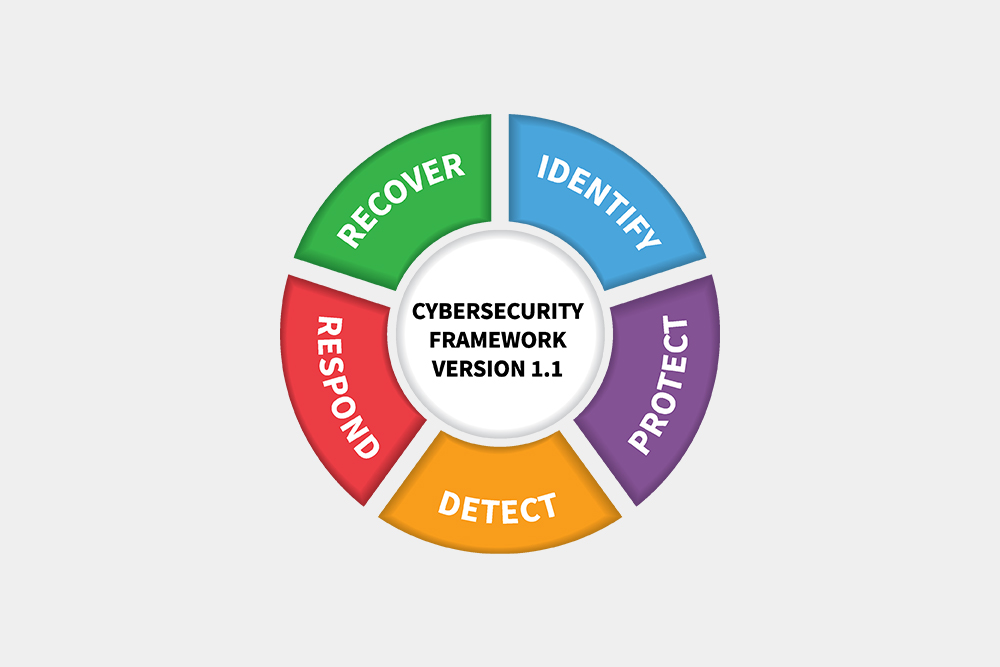
What is NIST and Why Should I Care?
You’ve heard other Managed Service Providers (MSPS) boasting about being NIST certified or following the NIST framework when applying cybersecurity programs, but you might have one question: What does that mean to me? The difference is night and day; it could mean everything. NIST 101 The National Institute of Standards and Technology (NIST), originating from…
Top 3 Personal Password Managers
You need a password manager You can’t remember every password for every service and tool you use—that’d be unrealistic. If you can, that means your passwords are too short, easy to remember, or are all the same. It’s a blatant vulnerability that any thief could capitalize on. You might be tempted instead to use your…
You’re Invited to the 2022 Cybersecurity Summit Series
Sponsored by Cooperative Systems Your business is at risk of a cyberattack In today’s threat landscape, more and more businesses are becoming vulnerable to threat actors. As technology rapidly evolves, you’ll need to stay ahead of the curve to protect yourself and your company’s integrity in the eyes of your clients and business partners. At…
What is a DDoS Attack, and What Do I Need to Know Right Now?
A DDoS attack is always bad news, and terrifyingly commonplace in our current world. In Q1 of 2022 alone, the Kaspersky DDoS Intelligence system reported approximately 91,052 global DDoS attacks have been launched so far. To make matters worse, Kaspersky also reports 44.34% of all DDoS attacks had their sights set on US-sourced organizations, which…
May 5th is World Password Day — is Yours Secure?
Did you know one of the easiest vulnerabilities for a cybercriminal to target when infiltrating your system is your password? 81% of 2021 US data breaches were caused by weak passwords with high credentials according to the Verizon 2021 Data Breach Investigation Report (DBIR). They’re a common human error, but the reason we do it…
Economic Sanctions vs Cybersecurity
With growing tensions between the Ukraine and Russia, and the US’s responsive economic sanctions on Russia, you may be surprised to learn how much this can affect the future of cybersecurity. It may not be on the forefront of your mind, but that doesn’t make the impact any less palpable for businesses in the US,…
What are the Top 4 Things You Need to Know to Protect Your Bank from the Next Cyber Invasion?
Reading time: 8 minutes In an era of increased banking options and billions being made by Chase and Bank of America (among others), it shouldn’t surprise anyone that cybercriminals have made financial institutions a lucrative target. But unfortunately, robbing banks is never as easy (or as simple) as walking through the door. That’s just Hollywood…
What are the Top 3 Cybersecurity Events You Can’t Afford to Miss in 2022?
Read time: 9 minutes Whether you are looking for the latest technical expertise or are wanting to build strategic skills to advance your career, various cybersecurity events exist to help you do both. As technology advances and cyber threats increase in sophistication, it’s becoming increasingly essential for IT professionals to stay on top of the…
4 Cybersecurity Career Hacks: A Cheat Sheet for Cybersecurity
Read time: 10 minutes Cybersecurity is a hot topic today. Awareness of online threats, viruses, and hackers is on the rise. Like LinkedIn and Bose, big-name companies have fallen victim to cyber-attacks. But there’s a significant shortage of cybersecurity professionals to manage these increasingly urgent issues. Forbes estimated that there will be more than 3.5 million unfulfilled cybersecurity jobs by…
Why Isn’t Your Current Managed Services Provider Qualified ENOUGH…to Protect Your Company’s Data?
Reading time: 9 minutes The United States is at an elevated risk for ongoing malicious cyberattacks from abroad. Will they increase in frequency and intensity? Only time will tell. However, in the past seven years, we’ve had front row seats to several of Russia’s pre-meditated cyberattacks on the Ukraine’s virtual infrastructure. Some attacks are as…
SIEM: How Can it Protect Your Business from the Next Cybersecurity Attack?
Reading time: 7 minutes Cyber threats from abroad are on the rise and ransomware attacks are significantly increasing each year. It’s never been more vital to invest in your cybersecurity infrastructure than it is today. Malicious actors are intentionally capitalizing on our fears and insecurities during moments of crisis. The COVID-19 pandemic is a prime…